One key benefit of the Veeva suite of solutions is that security and permissions are pre-configured to support the solution and highly configurable. This is great for your company from a compliance standpoint, but it can also introduce complexity that can be difficult to manage if not planned effectively from the beginning. You need to ensure that your users can access the correct data at the appropriate stage in the process, but you also need to protect and control that data to ensure that only authorized users have that access.
User access is a critical area to understand thoroughly as it impacts every area of your compliant, validated solution. So how do you manage it? Is there an internal team who has the skill, time, and knowledge to understand each layer of the access approach? Or are you using the approach of “well, the vendor validated this, so it is probably fine…”? Over many projects, fme has developed and refined a controlled and systematic method for assessing, planning, executing, and testing your user’s data access permissions to ensure you are in control of the access to your data, and get the most of the Veeva solutions.
Let’s take a look.
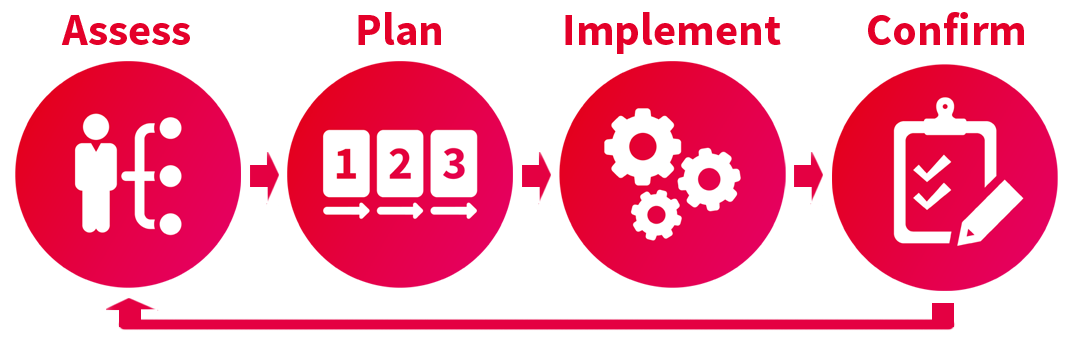
Assessment: Understand your permission set requirements
The first step is to get a detailed understanding of the permissions you will need. Your administration team and process owners should evaluate your existing structure to determine if the current licensing model and security configurations are working efficiently for your company. Review the following areas to identify opportunities:
- Security Roles define the specific access allowed in the system for each user
- Permissions Sets allow granular access to data and content
- User Roles dictate the roles automatically assigned to user depending on scope (for example: Approver role for a specific department)
- Lifecyle permissions determine which User Roles have access or can perform specific functions at different points in the document/record lifecycle
- Possible integrations to automate the user profile creation and management process
As you know there is a lot to consider here! You are looking for any gaps, overlaps, or conflicts between these areas.
Planning: Define required permission sets
With a clear understanding of the existing permissions settings and requirements, you can start to build a comprehensive permission matrix detailing who needs what level of access in each area. It is important to consider which user roles require holistic data access and which users’ roles require lifecycle-state-specific access. Access should be managed to allow completion of work responsibilities while also ensuring necessary oversight of sensitive materials.
In fme’s projects, once we identify existing improvement opportunities and develop a full permission matrix, we test the configuration changes to verify the defined requirements are met. We then review the recommendations and key benefits with the team leadership to determine the path forward. We work within your change management requirements to ensure control of the overall impact to users, training materials, in-progress workflows, and existing content. We document all this information in our Implementation Plan.
At the end of your planning process, you will have a robust, methodical Implementation Plan that your company can leverage within your change control and validation processes. This plan should also have provisions in place for future change. No system is static forever, so be sure to build in a controlled revision process for additions, edits, and deletions as you continue to grow and evolve.
Implementation Phase
After the plan above is agreed upon and ready for execution, it is essential to configure and fully test the updates in the validation environment. Review your permissions matrix and ensure that every point is tested for both what is allowed and for what should not be allowed . Do approved users and roles have access, and are all others blocked? Use your documentation to plan your testing to make sure your business needs are met. If you discover any issues or required adjustments, be sure to correct the issue, retest, and add the changes to the plan in a trackable process.
We’ve seen many first-pass configurations work perfectly until ‘white-hat’ testing exposes unexpected access allowed in critical areas. In fme’s methodology, we start with clearly defined documentation of what will be maintained, updated, or eliminated based on the approved plan. We then execute rigorous testing to verify that the changes provide the desired results. The test results are then summarized, documented and approved by our client team. With these changes tested and approved in the validation environment, we then plan and execute the same process for the production Vault.
Post Implementation Phase
Other elements that are often given minimal attention include training, post-implementation monitoring, and verification. Take the time to confirm the change is adopted smoothly by the end users, and all members of the admin team understand the changes and the reasons for them. Provide written procedures to ensure that optimized settings and profile assignments continue to be utilized as planned. Any additional changes should always be documented, reviewed, and approved.
With any change within complex systems, there are always unexpected combinations of variables that provide unplanned results. Don’t assume everything will go perfectly and plan some time for real-time fire drills and critical adjustments. If you do everything perfectly and don’t need that time, super! But if you do, you’ll be thankful you have the room for it.
When we work with our customers, we agree upon a specific period of post-implementation support to address any challenges encountered with the changes in production. We also train both users and admin teams, providing detailed documentation that can be referenced at any time. Beyond the end of the current project, we maintain a consistent communication cadence, so we are available for further updates or planned changes down the road. We also recommend periodic reviews to verify that established configurations match your evolving needs, and there are no outstanding changes waiting to be made. Our customers appreciate that we document and leverage the system and process knowledge gained during our engagements to help streamline future projects .
Conclusion
Permissions and access control are basic components of any system and should always be given appropriate attention. Ensure your team has the experience to consider all situations so you don’t leave security concerns and questions unanswered. These challenges will multiply over time if not addressed. With a complete permission structure defined that meets your specific business needs, you will ensure that your users have access to the data and workflows they need to do their jobs.
If you have any questions or concerns, please reach out to fme’s team of Veeva certified configuration experts to help you with your security management. Our proven step-by-step approach will show that it’s possible to leverage the robust configurability of the Veeva solution to serve your user and compliance needs with a consistent framework that is replicable for future business scenarios.
About the author
Amanda Hancock is a Principal Consultant with the Life Sciences business unit at fme US. She has over 20 years of experience in the Life Science industry, working in the clinical research and diagnostics sectors. Amanda started her career in 2000 as Research Assistant at The Ohio State university and later worked in the roles of QC Analyst, Quality Assurance Manager, and Quality Assurance Director before joining fme in 2022. In addition to being a Certified Quality Auditor (ASQ), Amanda is a Veeva Vault trained professional holding Associate Administrator certifications in Veeva Vault Platform, Veeva Vault QualityDocs, Veeva Vault QMS, Veeva Vault Submissions, and Veeva Vault Submissions Archive.
 fme AG
fme AG fme SRL
fme SRL